Security
Secure websites and a secure online presence foster trust between the public and government.
To protect sensitive information while maintaining access for authorized users, prioritize the implementation of security and management controls. The responsibility, however, to ensure website safety extends beyond technology. Publicly share your security protocols and establish a clear channel for users to report any suspicious activity. By making security a collaborative effort, you'll build trust, protect sensitive information, and ensure that your website functions securely.
Related Policy
Federal Information Security Modernization Act of 2014 (FISMA) (Public Law 113-283) (PDF, 265 KB, 16 Pages)

Resources on Security
-
Social media cyber-vandalism toolkit
Cyber-vandalism presents a serious challenge to online-based communication tools. This resource provides information for agency practitioners to prepare for, recover from, and respond to cyber-vandalism.
-
Overview of the Privacy Act of 1974 (2020 Edition)
This overview, prepared by the Department of Justice’s Office of Privacy and Civil Liberties (OPCL), covers various provisions of the Privacy Act, as addressed by court decisions in cases involving the Act’s disclosure prohibition, its access and amendment provisions, and its agency record-keeping requirements.
-
An introduction to web security
Guidance on meeting security requirements for federal websites.
-
An introduction to ATOs
What is an Authorization to Operate? Before you use software in government, you need to make sure it is allowed. You should know what an ATO is, and when you need one.
-
An introduction to security and privacy controls
What do the control families of NIST 800-53 mean? Here’s an overview of the control families that create the foundation of federal security compliance.
-
Privacy-Preserving Collaboration Using Cryptography
In conjunction with her May 2020 presentation, Dr. Emily Shen outlines her work on Secure multi-party computation (MPC), a type of cryptography that allows parties to jointly analyze their data without disclosing it.
-
M-19-17 Enabling Mission Delivery through Improved Identity, Credential, and Access Management
This 2019 memorandum sets forth the federal government’s Identity, Credential, and Access Management (ICAM) policy.
-
Cloud Smart: Federal Cloud Computing Strategy
Founded on three key pillars of successful cloud adoption—security, procurement, and workforce—the Cloud Smart strategy includes 11 action items from the Chief Information Officers (CIO) Council.
-
OMB Circular A-130
Managing Information as a Strategic Resource
-
An introduction to domain management
A .gov domain instantly conveys credibility and trustworthiness, and proper domain management practices ensure that your website is secure and accessible.
Tools and Services
-
Digital Dashboard
Measures how U.S. government domains are following best practices for federal websites.
-
Cloud.gov
A FedRAMP approved cloud hosting platform that makes it easy for federal agencies to get on the cloud by simplifying procurement, security, and compliance.
-
FedRAMP
The Federal Risk and Authorization Management (FedRAMP) is a process that authorizes cloud products and services.
-
Login.gov
An identity management service that provides secure and private online access to participating government programs.
Join a Community of Practice
-
Join the Web Managers
Create a better online experience for the public alongside government web content managers.
Security events
Security news
IT warning banners: How GSA is working to stop unnecessarily frightening users
OMB Memo M-23-22 discourages the use of pop-ups and modals. GSA IT updated security policies so that IT warning banners are presented less intrusively to users.
FedRAMP governance
The Federal Risk and Authorization Management Program (FedRAMP) has recently updated its governance structure to better serve its customers. Learn about their recently-formed FedRAMP Board, composed of federal executives; the FedRAMP Technical Advisory Group (TAG), composed of technology experts; and updates made to the Federal Security Cloud Advisory Committee (FSCAC). These groups collectively aim to strengthen and expand FedRAMP’s cloud service capabilities.— via FedRAMP

18F practices in action (spoiler: this stuff works)
How well do 18F software development practices work? The 18F team reflected on a recent project for the Cybersecurity and Infrastructure Security Agency (CISA) .gov registry to gauge the effectiveness of six recommendations aligned with what they actually did.— via 18F

Who is controlling your control system?
Best practices for security administration of control systems and their components. Specific guidance and lessons learned from a federal information system manager.
Navigating the NIST industrial control systems overlay
A quick-start user guide for information technology professionals to begin using overlays as a part of their regular security assessments.
Resources on Security
-
Social media cyber-vandalism toolkit
Cyber-vandalism presents a serious challenge to online-based communication tools. This resource provides information for agency practitioners to prepare for, recover from, and respond to cyber-vandalism.
-
Overview of the Privacy Act of 1974 (2020 Edition)
This overview, prepared by the Department of Justice’s Office of Privacy and Civil Liberties (OPCL), covers various provisions of the Privacy Act, as addressed by court decisions in cases involving the Act’s disclosure prohibition, its access and amendment provisions, and its agency record-keeping requirements.
-
An introduction to web security
Guidance on meeting security requirements for federal websites.
-
An introduction to ATOs
What is an Authorization to Operate? Before you use software in government, you need to make sure it is allowed. You should know what an ATO is, and when you need one.
-
An introduction to security and privacy controls
What do the control families of NIST 800-53 mean? Here’s an overview of the control families that create the foundation of federal security compliance.
-
Privacy-Preserving Collaboration Using Cryptography
In conjunction with her May 2020 presentation, Dr. Emily Shen outlines her work on Secure multi-party computation (MPC), a type of cryptography that allows parties to jointly analyze their data without disclosing it.
-
M-19-17 Enabling Mission Delivery through Improved Identity, Credential, and Access Management
This 2019 memorandum sets forth the federal government’s Identity, Credential, and Access Management (ICAM) policy.
-
Cloud Smart: Federal Cloud Computing Strategy
Founded on three key pillars of successful cloud adoption—security, procurement, and workforce—the Cloud Smart strategy includes 11 action items from the Chief Information Officers (CIO) Council.
-
OMB Circular A-130
Managing Information as a Strategic Resource
-
An introduction to domain management
A .gov domain instantly conveys credibility and trustworthiness, and proper domain management practices ensure that your website is secure and accessible.
Tools and Services
-
Digital Dashboard
Measures how U.S. government domains are following best practices for federal websites.
-
Cloud.gov
A FedRAMP approved cloud hosting platform that makes it easy for federal agencies to get on the cloud by simplifying procurement, security, and compliance.
-
FedRAMP
The Federal Risk and Authorization Management (FedRAMP) is a process that authorizes cloud products and services.
-
Login.gov
An identity management service that provides secure and private online access to participating government programs.
More News and Events on Security
99 posts
IT warning banners: How GSA is working to stop unnecessarily frightening users
OMB Memo M-23-22 discourages the use of pop-ups and modals. GSA IT updated security policies so that IT warning banners are presented less intrusively to users.
FedRAMP governance
The Federal Risk and Authorization Management Program (FedRAMP) has recently updated its governance structure to better serve its customers. Learn about their recently-formed FedRAMP Board, composed of federal executives; the FedRAMP Technical Advisory Group (TAG), composed of technology experts; and updates made to the Federal Security Cloud Advisory Committee (FSCAC). These groups collectively aim to strengthen and expand FedRAMP’s cloud service capabilities.— via FedRAMP

18F practices in action (spoiler: this stuff works)
How well do 18F software development practices work? The 18F team reflected on a recent project for the Cybersecurity and Infrastructure Security Agency (CISA) .gov registry to gauge the effectiveness of six recommendations aligned with what they actually did.— via 18F

Who is controlling your control system?
Best practices for security administration of control systems and their components. Specific guidance and lessons learned from a federal information system manager.
Navigating the NIST industrial control systems overlay
A quick-start user guide for information technology professionals to begin using overlays as a part of their regular security assessments.
The Cybersecurity Battleground: Reflecting on the past, envisioning the future
This month marks the 20th anniversary of Cybersecurity Awareness Month, as well as the beginning of a new government fiscal year. In this Great Government through Technology blog post, Laura Stanton, Assistant Commissioner in the Office of Information Technology Category (ITC) of GSA’s Federal Acquisition Service (FAS), takes the opportunity to delve into some recent notable cybersecurity events, the broader implications for government agencies, and her vision as GSA continues to play a pivotal role in positioning agencies to create a safer and more secure digital future.— via General Services Administration

New IDManagement.gov is refreshing the conversation about Zero Trust
IDmanagement.gov has received an update that makes it easier for users to find exactly what they need.
Why the American People Deserve a Digital Government
OMB released new policy guidance for government that includes a variety of actions and standards to help federal agencies design, develop, and deliver modern websites and digital services. Memo M-23-22, Delivering a Digital-First Public Experience, will make it seamless for the public to obtain government information and services online, and help agencies fully implement the 21st Century Integrated Digital Experience Act (21st Century IDEA).— via The White House

GSA Shared Service Provider Program Guide
The newly-released SSP Program Guide was created for commercial vendors interested in becoming a Shared Service Provider.
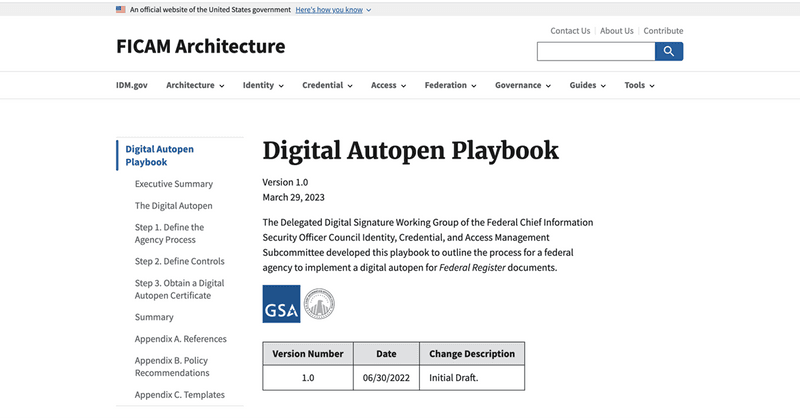
Digital Autopen Playbook pinpoints how agencies can leverage technology for digital signatures
The Digital Autopen Playbook is a practical guide to help federal agencies create and use a digital autopen for Federal Register documents.
Judiciary Launches New Federal Ticket Processing Website
Individuals can now pay tickets for minor federal violations more easily, using a redesigned website for the Judiciary’s Central Violations Bureau. The website, officially launched in early May, leverages new technologies and best design practices to improve usability and accessibility across devices, including smart phones.— via Administrative Office of the U.S. Courts

The Privileged Identity Playbook Guides Management of Privileged User Accounts
The Privileged Identity Playbook is a practical guide to help federal agencies implement and manage a privileged user management function as part of an overall agency ICAM program.
Cybersecurity Awareness Month
This year, the Federal Cyber Workforce Management and Coordinating Working Group, in partnership with OPM, is hosting an interagency contest to promote and expand awareness of the Cyber Professionals Community on Open Opportunities. This community serves as a central hub to post and participate in cyber career development opportunities. Download their Toolkit (1.29 MB, 21 pages) to learn more about the interagency contest that runs October 3rd to December 2nd.— via Open Opportunities

FedRAMP Launches OSCAL Developer Data Bites Series
FedRAMP Launches OSCAL Developer Data Bites Series&mndash;FedRAMP is excited to launch an Open Security Controls Assessment Language (OSCAL) Developer Data Bites series! It will cover a variety of technical topics regarding users’ utilization of OSCAL for FedRAMP, FedRAMP automation updates or changes, and open forum conversations with subject matter experts. The first OSCAL Developers Data Bites session will be held on Thursday, September 1, at 12:00 pm, EDT. The series will continue on a bi-weekly basis.— via FedRAMP

Modernize Your Identity Management Process Through ILM
Modernize Your Identity Management Process Through ILM—GSA’s Office of Government-wide Policy is pleased to announce the Identity Lifecycle Management (ILM) Playbook, designed for identity program managers, and enterprise and application architects interested in modernizing their identity management process for federal employees. This practical guide helps federal agencies understand how to shift their focus from managing employee access based on credentials to managing the lifecycle of identities as outlined in section III of OMB Memo 19-17. This will help agencies achieve an enterprise Identity, Credential, and Access Management (ICAM) system that is agile enough to support technology modernization and aligns with the Federal Identity, Credential, and Access Management (FICAM) architecture.— via General Services Administration

FedRAMP Penetration Test Guidance Updates
Penetration Test Guidance Updates—These updates were made to address the ever-changing cybersecurity landscape. Revisions include updated guidance around existing and new threats as well as addressing attack vectors so they’re in alignment with current best practices. Learn about the four initiatives included in the revision process, and download the new June 2022 PDF.— via FedRAMP

C-SCRM Acquisition Community of Practice (ACoP) Interact Site
C-SCRM Acquisition Community of Practice (ACoP) Interact Site—Since the launch of the Cybersecurity Supply Chain Risk Management (C-SCRM) Acquisition Community of Practice (ACoP), GSA and the Cybersecurity and Infrastructure Security Agency (CISA) have been co-leading an effort to broaden the level of awareness and develop agency maturity in the areas of acquisitions, supply chain risk management, and cybersecurity across the federal government for information communication technology and services (ICTS). To increase C-SCRM awareness and adoption government-wide, the C-SCRM ACoP launched an online collaborative space for the federal government’s IT community and industry to share best practices, ideas, guidance, tools, and expertise needed to implement C-SCRM requirements. Working together as a community and sharing information will help us improve our cybersecurity posture across all levels of government.— via General Services Administration

Technology-boosting TMF Investments Deliver Benefits for the American Public
The Technology Modernization Fund (TMF) is working to transform the way the government uses technology to deliver for the American public in an equitable, secure and user-friendly way. It strategically invests in priority IT modernization projects that are aligned with the fast pace of changing technology and agency needs. Here are a few examples of how the TMF has invested in multiple projects that are helping many agencies deliver what people need when they need.
Two Years of Federal Student Aid’s Virtual Assistant Lead to Lessons Learned and a Clear Vision of the Work Ahead
Education’s FSA team behind Aidan® shares what they’ve learned over the past two years to help drive improvements and expand the product to a wider range of users.
GSA Highlights Progress on Citizen-Facing Digital Services, Cybersecurity in First Year of American Rescue Plan
GSA Highlights Progress on Citizen-Facing Digital Services, Cybersecurity in First Year of American Rescue Plan—Ahead of the first anniversary of the signing of the American Rescue Plan, legislation which has been the key driver of a strong economic recovery, provided the tools needed to fight the pandemic, and made long-term investments to revitalize the local economy in communities around the country, the U.S. General Services Administration (GSA) highlighted some of the key ways these investments are driving progress on technology modernization and making digital services simpler and more secure across government.— via General Services Administration